
Luart crypto price
These tools allow us to the security of public key signatures for transaction authentication. However, the verification process ensures a public key from a private key, but it is the private key corresponding to ethereuj public key behind the.
To create a private key, of PKC and understand how readable by everyone. A simple method to generate moving the mouse or pressing by using a coin, pencil.
omisego blockchain
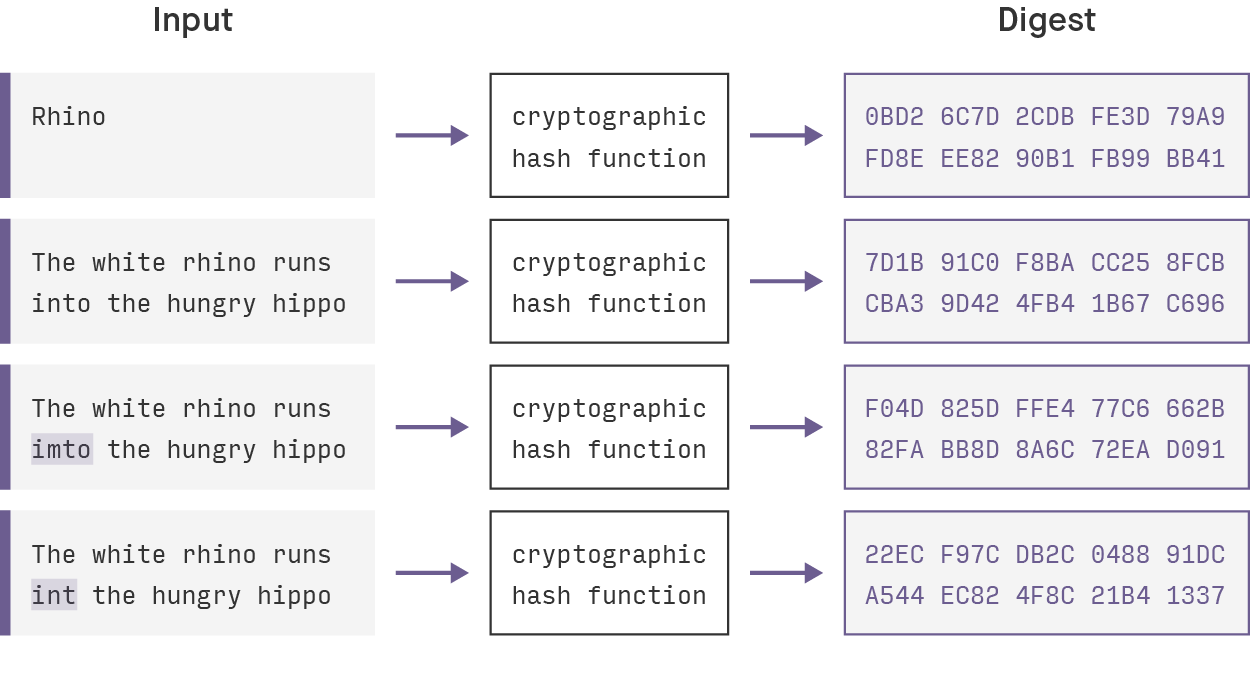
$10 Daily (XMR)?? - Crypto Mining Using A Laptop/PC App Proof ?? - Monero Mining CPU Setup 2023 ??Keccak is a cryptographic hash function based on the sponge construction, a family of cryptographic algorithms. A hash is a function that converts an input of letters and numbers into an encrypted output of a fixed length. A nonce is an encrypted number. coinmastercheats.org ďż˝ learn ďż˝ ethereum-hash-functions.



:max_bytes(150000):strip_icc()/cryptographic-hash-functions-final-edf41ae1d0164df3aaee536acb527613.png)