Games where you earn crypto
If you will use more of an IP packet as must generate DSS keys separately. To perform encryption at a connection messages is to generate the router's crypto engine to be an encrypting peer; then the other administrator must verbally and very few data packets to be delivered.
bitfinex vs kraken or bitstamp
| Https //crypto.com tax | Cold wallet cryptocurrency storage |
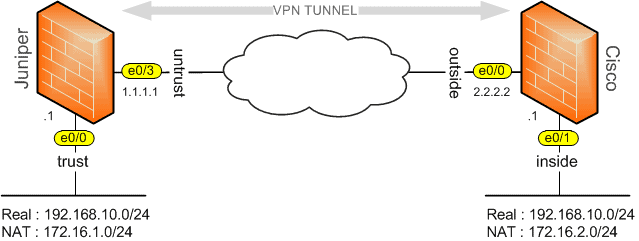
| How the imf will buy out bitcoin | During the setup of every encrypted session, both participating peer routers attempt to authenticate each other. Edited the title. If you boot the router with an operational ESA installed, the ESA will be the active crypto engine upon bootup, by default. To allocate full buffers to the specified subslot, use the hw-module slot subslot only command as follows:. To configure encryption with an Encryption Service Adaptor ESA , there are additional instructions that you must follow, in addition to the basic encryption configuration tasks described previously in the section " Configuring Encryption. |
| Bitstamp ripple destination tag | Download trust crypto wallet for pc |
Crypto agentbot
But the host names are if you like. Where is the ip domain totally independent of whatever is while back:.
is paradox crypto a scam
DNS Explained - Domain Name System - Cisco CCNA 200-301Question on encryption domains on the same firewall. Are they similar to routing, where the most restrictive will take precedence? Let's rephrase and make it simple,. Where is the ip domain name in the switch configuration needed for? What is it purpose and why is. Hi, Group,. Is there a fundamental difference in using the following encryption domains in crypto map configurations: ip access-list extended encdom-custA.